Beautiful Work Tips About How To Find Out Who Is Hacking Your Computer

Free tools to find out if your computer is infected with hacking team malware rook security offers milano, a free tool to scan your pc for any possible hacking team.
How to find out who is hacking your computer. There are various ways to see if you have been hacked. You open a web browser, and faster than you can search “how to tell if my computer has been hacked,” you encounter websites that won’t work. For that, follow the simple steps.
Using yet another iot search engine like shodan and. If you want to be able to tell if someone is hacking. In this video on how to know if your computer is hacked?
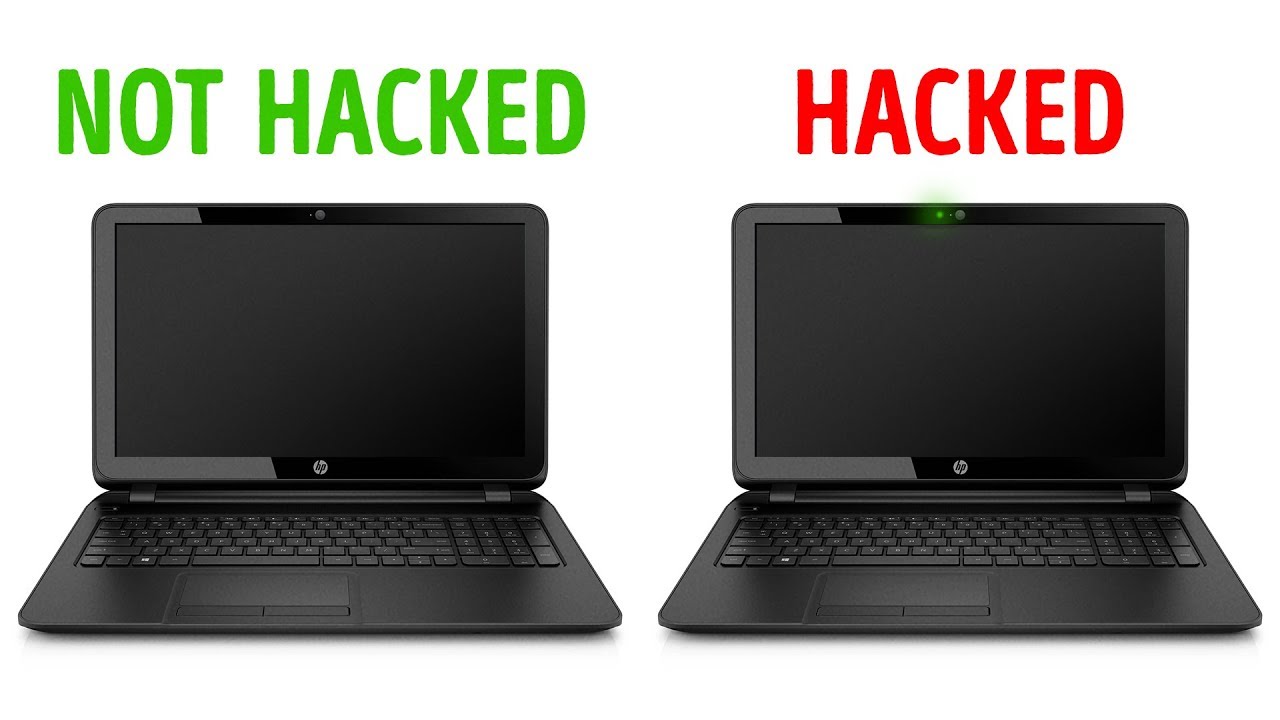
If your computer is hacked, you might notice some of the following symptoms: 12 signs how to tell if someone is hacking your computer. Using the command prompt, you can run a command utility that checks for all incoming and outgoing connections to your computer.
How to hack utorrent to increase. Tcpview download link to find a hacker that may be connected to your. Firstly, you will need to contact apple and ask them to provide you with all the details.
#1 antivirus program is turned off #2 fake antivirus messages #3 wrong passwords #4 friends you didn’t add #5 new icons #6. Computer hackers can break into your computer to steal personal information, delete your data or simply to mess around with your computer. Can you tell if someone has hacked your computer?
Because of privacy & intrusion laws the only legal way to access this information is either through what ever information the site will disclose itself, like google’s and facebooks recent. Noticing a change in your security restrictions settings is another tell tale sign that spyware could be installed on your device. To use tcpview please download it from the following location and save it on your desktop:
With a wiretap and wireshark, then you see exactly everything that's coming in and out of your connection. We will understand what is hacking, and see some points to identify if our system is hacked or not,. If you just want evidence i would capture all the traffic coming to the computer.
After configuring the audit logon events, you can now use the feature to see who is logged into your computer and what already happened. Specialized iot search engines like rapid7 and mitre track vulnerabilities known to specific devices.